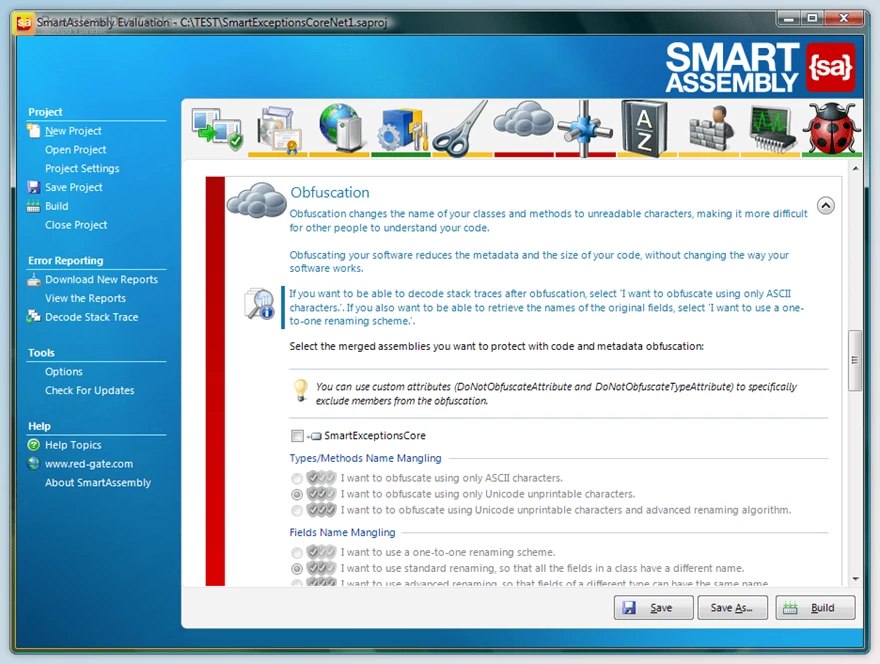
Red Gate SmartAssembly can decode the stack traces and generate the files of the .pdb containing information about the debugging. It permits the users and developers to debug the assembly into the IDE and get an entire stack trace if an exception occurs. It can even help a user and the developer to ensure that the user is automatically releasing the unneeded memory. Red Gate SmartAssembly is an obfuscator that can help protect the user program against alteration and reverse engineering processes. Suppose the user's entire company is resetting the IP embodied in the user application. In that case, it does not require the user C# or even the VB.NET code globally to be vulnerable. The user can receive extensive attributes of the obfuscation. It is also described as a loading code for the protection and improvement of the tools, which has multiple levels and is capable of protecting the user software and defending the software from the reverse engineering process.
Red Gate SmartAssembly permits the users on the developer to attach data that is custom to the reports obtained, such as log files and screenshots. It is a process by which the tool is captured and allows the users to focus more on the design process. It is also known to be an agent for the development which permits the users at the developers to create the existing cards in the assembler or even the sub-assemblies to configure parts that are new or sub-assemblies. The users are capable of developing a program in simple as well as flexible use of the language.
Red Gate SmartAssembly can provide users with a compelling script language to define the templates using the component and the available features. A robust machine design and function are also provided by the smart assembly, such as library management and other standard functions and components. It can define the automation rules that are required with the use of the features as well as a standard component along with assemblies. It can define the project along with its templates and the data to be reused, copied automatically, and even renamed along with all the manufacturing files that are copied to the newly created projects.
Key Features of Red Gate SmartAssembly :
- Name mangling: It can change the names that belong to the methods as well as the fields to make it hard to understand by others about their purpose.
- Control flow obfuscation: It can convert the codes right inside the methods to make it difficult to see the application as how it works.
- Reference Dynamic proxy: It is described to be an ability that has the power to create a proxy for all the calls to method the outside of the user assembly and make it harder to find external calls.
- String encoding: in this feature strings are being encoded to be used in the user software to hide information as well as the SQL queries.
- Resources compression and encryption process: This feature can compress and encrypt resources that are managed to make them harder to understand, reduce the size of the assembly, and make it more comfortable at the same time suitable.
- Pruning: In this feature, non-useful metadata is being removed to make codes harder, reverse the engineering process, reduce their assembly’s size as well and improve the time of the loading.
- Merging of the dependencies: It can take all the DLLs and merge them into one main assembly so that the user does not have to load many different files of DLL for them to be obfuscated.
- Declaring of the obfuscation: In this method, a member is excluded from obfuscation with the use of attributes that are custom in nature directly in the user code.
Click on the links below to Download the latest version of Red Gate SmartAssembly with Keygen!

 Red Gate SmartAssembly v8.4.6.7042 (14 May 2026) + Keygen.rar (Size: 11.0 MB - Date: 5/16/2026 11:32:25 AM)
Red Gate SmartAssembly v8.4.6.7042 (14 May 2026) + Keygen.rar (Size: 11.0 MB - Date: 5/16/2026 11:32:25 AM) Red Gate SmartAssembly v8.4.5.6931 (22 Apr 2026) + Keygen.rar (Size: 11.0 MB - Date: 4/25/2026 11:51:21 AM)
Red Gate SmartAssembly v8.4.5.6931 (22 Apr 2026) + Keygen.rar (Size: 11.0 MB - Date: 4/25/2026 11:51:21 AM) Red Gate SmartAssembly v8.4.4.6815 (27 Mar 2026) + Keygen.rar (Size: 11.0 MB - Date: 4/3/2026 12:33:11 PM)
Red Gate SmartAssembly v8.4.4.6815 (27 Mar 2026) + Keygen.rar (Size: 11.0 MB - Date: 4/3/2026 12:33:11 PM)







![FREE Download DevExpress Universal Complete [.Net Components] v25.2.5.26075 (21 Mar 2026) + Documentation + Patcher](https://downloaddevtools.com/filemanagercontent/files/1/prolistnormal/124-banner.png)

9/14/2020 8:25:32 PM
New keygens have been added.
thank you 👍
9/14/2020 11:59:38 AM
Keygen will not work. It is for version 6 not version 7.
New keygens have been added.
9/13/2020 8:09:43 PM
Keygen will not work. It is for version 6 not version 7.