
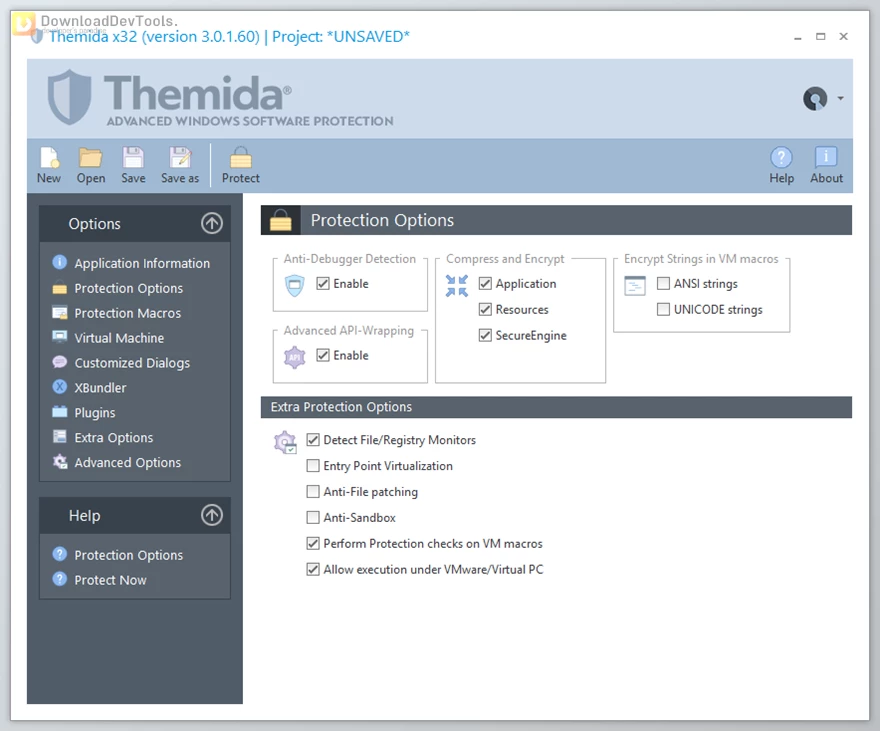
 Oreans Technologies Themida v3.2.2.22 (x86 & x64) + CRACK.rar (Size: 64.6 MB - Date: 11/26/2025 8:30:49 AM)
Oreans Technologies Themida v3.2.2.22 (x86 & x64) + CRACK.rar (Size: 64.6 MB - Date: 11/26/2025 8:30:49 AM) Oreans Technologies Themida v3.1.8.0 (x86 & x64) + CRACK.rar (Size: 63.3 MB - Date: 11/26/2025 8:30:47 AM)
Oreans Technologies Themida v3.1.8.0 (x86 & x64) + CRACK.rar (Size: 63.3 MB - Date: 11/26/2025 8:30:47 AM) Oreans Technologies Themida v3.1.4.18 (x86 & x64) + CRACK.rar (Size: 58.7 MB - Date: 11/26/2025 8:30:45 AM)
Oreans Technologies Themida v3.1.4.18 (x86 & x64) + CRACK.rar (Size: 58.7 MB - Date: 11/26/2025 8:30:45 AM) Oreans Technologies Themida v3.0.4.0 (x86 & x64) + CRACK.rar (Size: 56.4 MB - Date: 11/26/2025 8:30:44 AM)
Oreans Technologies Themida v3.0.4.0 (x86 & x64) + CRACK.rar (Size: 56.4 MB - Date: 11/26/2025 8:30:44 AM)
Files Password : DownloadDevTools.ir
Note
Download speed is limited, for download with higher speed (2X) please register on the site and for download with MAXIMUM speed please join to our VIP plans.
Join our Telegram group
Discover free tools, limited-time offers, and stay updated with the latest software we release.
Discover free tools, limited-time offers, and stay updated with the latest software we release.








10/17/2023 11:02:34 AM
Please update to latest version. Release: 3.1.3.0 Date: 26-Apr-2022
5/14/2021 10:36:48 PM
کل اگر طبی بودی سر خود دوا بکردی خودشو کرک کردن خخخخ