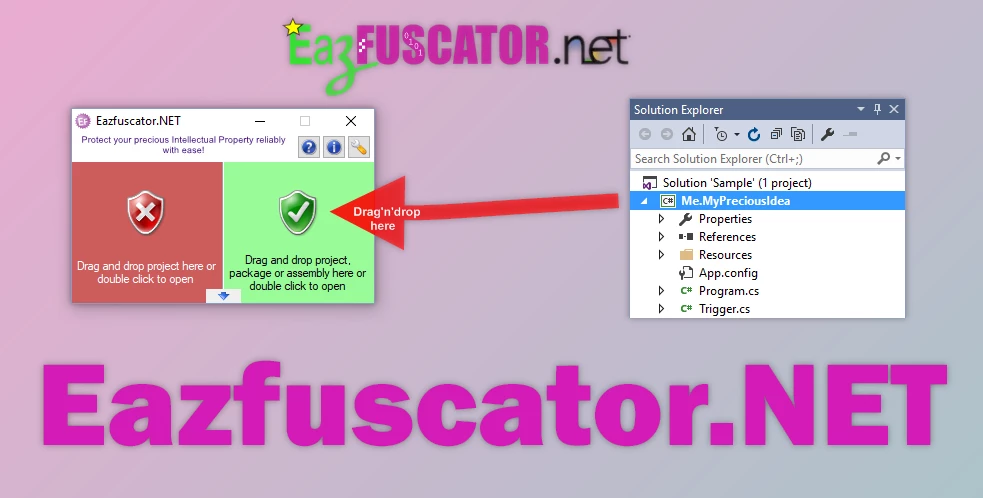
Eazfuscator.NET is a sophisticated tool designed specifically for the .NET platform. It safeguards the intellectual property embedded in software. This protection not only boosts the software's commercial value but also gives developers an edge over competitors. It's essentially like having a reliable partner in software development who handles the complexities of security without any fuss.
Using Eazfuscator.NET is incredibly straightforward. The obfuscation process is automated once it's set up with your Visual Studio project. Every time you build your project in the Release configuration, the software automatically obfuscates the code, so you can focus more on coding and less on protecting your project. It simplifies the development process by removing the need for constant attention to security details.
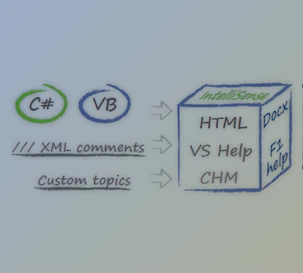
The tool is also highly customizable, allowing developers to tailor the obfuscation features to their needs using .NET obfuscation attributes. This approach is simpler and more stable than complex configuration files. Eazfuscator.NET also comes with comprehensive documentation, making it easy to get the most out of its features.

Key Features of Eazfuscator.NET :
- Automatic Protection: This plugin integrates with your Visual Studio project to provide automatic obfuscation with every
- Release build, simplifying the process of securing your code.
- Easy to Use: A simple setup is required, and the tool runs seamlessly in the background, requiring no further intervention.
- Customizable Settings: This option offers flexibility through the use of .NET obfuscation attributes, which allows for specific settings adjustments without the hassle of complex configurations.
- Robust Documentation: Comprehensive guides and documentation are available to help users navigate the tool's features and maximize its capabilities.
Click on the links below to Download the latest version of Eazfuscator.NET with CRACK!
 Eazfuscator.NET v2026.1 (07 May 2026) + CRACK.rar (Size: 21.0 MB - Date: 5/21/2026 12:56:54 PM)
Eazfuscator.NET v2026.1 (07 May 2026) + CRACK.rar (Size: 21.0 MB - Date: 5/21/2026 12:56:54 PM) Eazfuscator.NET v2025.3 (17 Nov 2025) + CRACK.rar (Size: 20.0 MB - Date: 12/27/2025 1:31:47 PM)
Eazfuscator.NET v2025.3 (17 Nov 2025) + CRACK.rar (Size: 20.0 MB - Date: 12/27/2025 1:31:47 PM) Eazfuscator.NET v2025.2 (03 Oct 2025) + CRACK.rar (Size: 19.9 MB - Date: 11/26/2025 8:28:01 AM)
Eazfuscator.NET v2025.2 (03 Oct 2025) + CRACK.rar (Size: 19.9 MB - Date: 11/26/2025 8:28:01 AM)





![FREE Download DevExpress Universal Complete [.Net Components] v25.2.5.26075 (21 Mar 2026) + Documentation + Patcher](https://downloaddevtools.com/filemanagercontent/files/1/prolistnormal/124-banner.png)







4/19/2022 4:17:10 AM
Can this be updated?
4/11/2022 5:43:45 AM
Would love to get the updated version if possible: Eazfuscator.NET 2022.1
1/16/2021 7:45:18 PM
the download link is incorrectly pointing to a different item.
Thank you for your notification, please download again
1/16/2021 12:28:35 AM
the download link is incorrectly pointing to a different item.