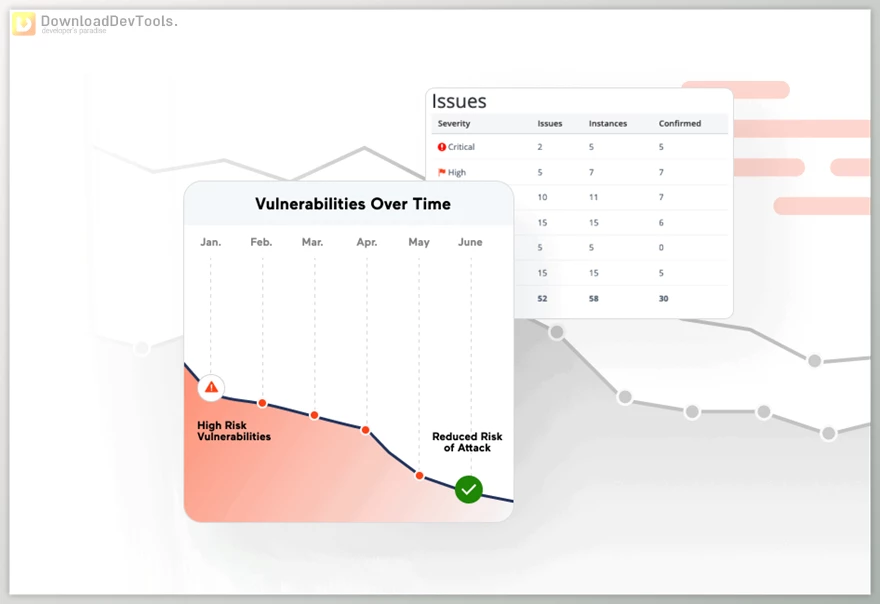
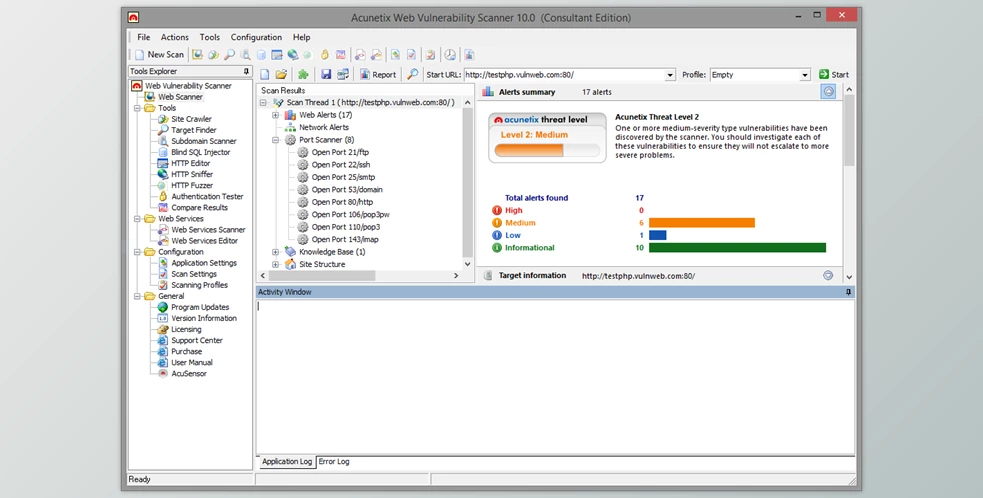
Acunetix Web Vulnerability Scanner offers a comprehensive solution to swiftly identify and rectify vulnerabilities in your web applications. By seamlessly blending Dynamic Application Security Testing (DAST) with Interactive Application Security Testing (IAST), Acunetix detects over 7,000 vulnerabilities, including critical threats like OWASP Top 10, SQL injections, XSS, misconfigurations, and more. With lightning-fast scans, you receive actionable results in minutes, allowing you to prioritize high-risk vulnerabilities and schedule scans effortlessly.
Streamlining the remediation process, Acunetix Web Vulnerability Scanner eliminates false positives and provides precise vulnerability locations, enabling developers to pinpoint and fix security flaws efficiently. By offering detailed remediation guidance, it empowers developers to address vulnerabilities independently, saving valuable time and resources. Moreover, Acunetix’s versatility extends to scanning diverse environments, including single-page applications, script-heavy sites, password-protected areas, and unlinked pages, ensuring no part of your application remains unscanned and vulnerable.
Integrating seamlessly into your development workflow, Acunetix Web Vulnerability Scanner enables developers to take proactive security measures by integrating with popular tools like GitHub, JIRA, Jenkins, and more. With Acunetix Web Vulnerability Scanner, you can effortlessly integrate web security into your development process, ensuring robust protection against emerging threats while maximizing efficiency and peace of mind.
Key Features of Acunetix Web Vulnerability Scanner :
- Detect over 7,000 vulnerabilities including OWASP Top 10, SQL injections, XSS, misconfigurations, exposed databases, and more
- Lightning-fast scans provide actionable results in minutes
- Automatically prioritize high-risk vulnerabilities
- Schedule one-time or recurring scans
- Pinpoint vulnerability locations and provide precise remediation guidance
- Eliminate false positives to save time and resources
- Scan diverse environments including single-page applications, script-heavy sites, password-protected areas, and unlinked pages
- Integrate seamlessly with popular development tools like GitHub, JIRA, Jenkins, and more
Click on the links below to Download the latest version of Acunetix Web Vulnerability Scanner with CRACK!
 Acunetix Web Vulnerability Scanner v15.2.2 for Windows + CRACK.rar (Size: 213.2 MB - Date: 11/26/2025 6:28:43 AM)
Acunetix Web Vulnerability Scanner v15.2.2 for Windows + CRACK.rar (Size: 213.2 MB - Date: 11/26/2025 6:28:43 AM) Acunetix Web Vulnerability Scanner v14.9.220713150 for Windows & Linux + CRACK.rar (Size: 457.5 MB - Date: 11/26/2025 6:28:39 AM)
Acunetix Web Vulnerability Scanner v14.9.220713150 for Windows & Linux + CRACK.rar (Size: 457.5 MB - Date: 11/26/2025 6:28:39 AM) Acunetix Web Vulnerability Scanner v14.7.220401065 for Windows + CRACK.rar (Size: 202.3 MB - Date: 11/26/2025 6:28:29 AM)
Acunetix Web Vulnerability Scanner v14.7.220401065 for Windows + CRACK.rar (Size: 202.3 MB - Date: 11/26/2025 6:28:29 AM) Acunetix Web Vulnerability Scanner v14.6.211220100 for Windows + CRACK.rar (Size: 183.0 MB - Date: 11/26/2025 6:28:25 AM)
Acunetix Web Vulnerability Scanner v14.6.211220100 for Windows + CRACK.rar (Size: 183.0 MB - Date: 11/26/2025 6:28:25 AM)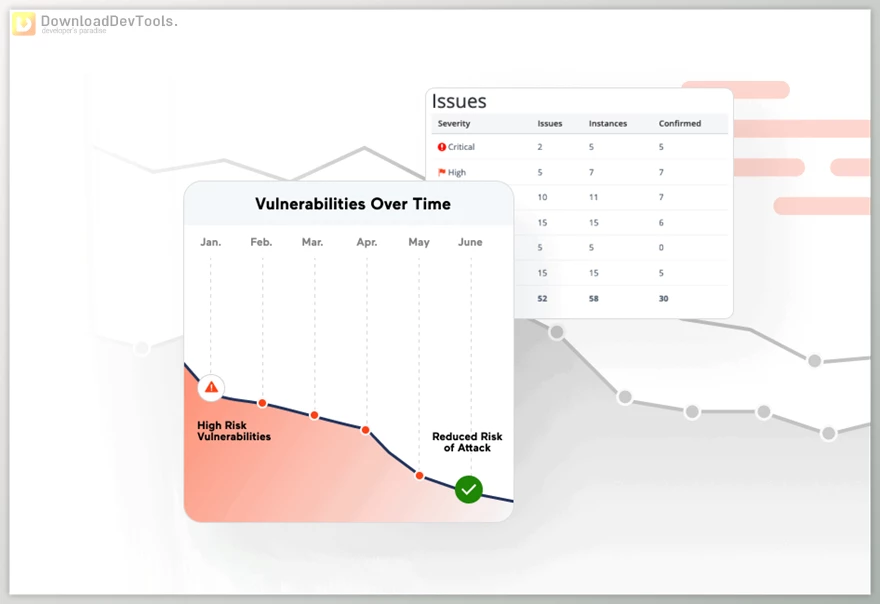













9/9/2023 3:59:14 PM
Would it be possible to get this updated to current please?